Simple Ways to Shield Your Team Against Viruses and Malware
Malware and viruses pose a threat to businesses. These programs are designed to disrupt normal operations by compromising sensitive company data. However, with a few proactive measures, you can protect your team’s/business devices and data. Some of the steps you can take include implementing robust access controls, regular security assessments, encrypting data, monitoring end-point data, and raising security awareness.
Contents
Understanding and Detecting Viruses
Viruses are programs (malicious software) that cause data damage in your computer systems. They target specific files and make a copy. Some are harmless, while others destroy the critical components of your computer systems. The signs and symptoms of virus infection are loss of bandwidth or information, exposure to dangerous software, loss of performance, and breach of privacy.
Solutions for Virus Protection
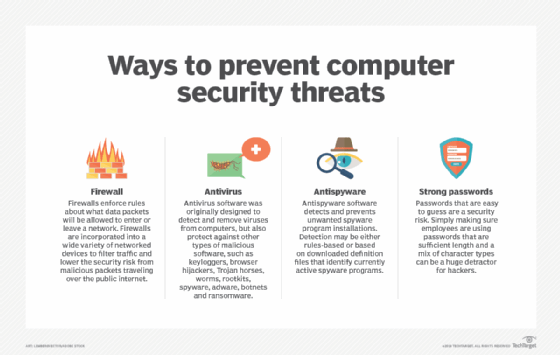
Antivirus software can be an effective tool in a business. One must ensure the software is compatible with the operating system, as well as other devices. Another approach is to implement robust email filtering techniques to protect the entry points. For instance, you can filter server and client emails to identify phishing attempts.
In the heart of the diverse state of Minnesota, where major projects thrive, enterprises fortify their defenses against cyber hazards by engaging in partnerships with cybersecurity specialists, including managed IT professionals situated in Minneapolis. These experts are known to have wide experience in providing technical assistance in detecting and diagnosing potential issues early on, assessing areas within the business that may be vulnerable to threats, and implementing cutting-edge technology to ensure data protection.
Understanding and Detecting Malware
Let’s look at the different types of malware and their behaviors.
Viruses
They affect program files, causing instability in the computer systems. Sometimes, they can attack the network or email attachments.
Worms
They spread across networks, causing a disruption. Worms can compromise your computer systems or spread across the entire network.
Ransomware
They demand a “ransom” in exchange for restored access (decryption keys). Ransomware spreads through compromised websites, email attachments, etc.
Trojans
They trick users into taking a legitimate action to steal sensitive information. Once installed, they become the backdoor for remote access.
Some tell-tale signs of malware include sluggishness in your computer systems, unexplained network traffic, warning alerts from your antivirus, pop-up ads, and usual system activity.
Solutions for Malware Protection
To enhance the security system across all devices, you need anti-malware software with real-time protection features. When choosing a provider, pay attention to detection capability, rates, and compatibility with your OS. To ensure real-time protection, you should configure the settings – specify the files to monitor, and adjust the sensitivity level.
Other than that, you must conduct regular malware scans and remove any detected threats. You should schedule scans based on the usage level of the computer systems – weekly, bi-weekly, etc.
Finally, you ought to implement endpoint security measures to prevent malware infiltration. A reputable solution will enable real-time protection by monitoring outgoing network traffic. Remember to configure your firewalls to block malicious connections.
Conclusion
Deploying comprehensive security measures can help you address the damage that comes with virus and malware attacks. You should utilize antivirus software to detect and protect your sensitive business information. Each threat requires a different approach, so you should educate your team on how to keep tabs on the latest trends. It’s also vital that you stay informed about emerging threats and best practices and adapt the latest security measures accordingly.